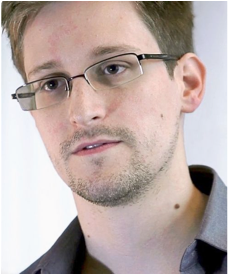
 When Edward Snowden disclosed the NSA’s activities, many people came to realize that network systems can be misused, even though this was always the case. People just realized what was possible. What happened next was a concerted effort to protect protect data from what has become known as “pervasive surveillance”. This included development of a new version of HTTP that is always encrypted and an easy way to get certificates.
When Edward Snowden disclosed the NSA’s activities, many people came to realize that network systems can be misused, even though this was always the case. People just realized what was possible. What happened next was a concerted effort to protect protect data from what has become known as “pervasive surveillance”. This included development of a new version of HTTP that is always encrypted and an easy way to get certificates.
However, when end nodes hide everything from the network, not only can the network not be used by the bad guys, but it can no longer be used by the good guys to either authorize appropriate communications or identify attacks. A example is spam. Your mail server sits in front of you and can reject messages when they contain malware or are just garbage. It does that by examining both the source of the message and the message itself. Similarly, anyone who has read my writing about Things knows that the network needs just a little bit of information from the device in order to stop unwanted communications.
I have written an Internet Draft that begins to establish a framework for when and how information should be shared, with the idea being that information should be carefully shared with a purpose, understanding that there are risks involved in doing so. The attacks on Twitter and on krebsonsecurity.com are preventable, but it requires us to recognize that end nodes are not infallible, and they never will be. Neither, by the way, are network devices. So long as all of these systems are designed and built by humans, that will be the case. Each can help each other in good measure to protect the system as a whole.
Photo of Edward Swowden By Laura Poitras / Praxis Films, CC BY 3.0