
You have to have been hiding under a rock over the last week not to have heard about scare stories about kids being tormented by perverts and others being violently extorted through various Ring products. Not exactly what you were expecting from your security product, was it?
With so many reports of IoT devices being vulnerable to attack, one might leap to the idea that the Ring device itself has been poorly designed, and thus broken into, but one would be wrong. That is because, like so many IoT devices, Ring products make use of the cloud to offer a service. Here’s how it all works.
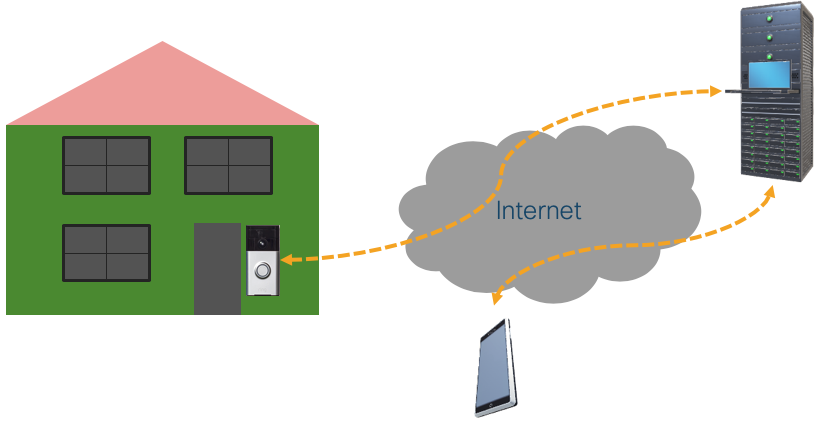
When you establish an account, you are doing this not on the doorbell, but on a service somewhere on the Internet to which the doorbell connects. This is evident, because when you go to ring.com, you can log in with the account that you have previously established in the app.
Later during device setup, the doorbell is registered with the service, using the phone’s setup app. This is likely the only time the phone would directly communicate with the doorbell. All other communications flow through the service, as drawn above.
So how did someone else get to control your device? If you are not using two factor authentication, an attacker requires two pieces of information to control your device: your email address and your password. Your email address can easily have appeared in public if you have joined a public mailing list, or had made a comment on a poorly designed web site. An attacker may also be able to guess your password if you have used that same password on a service that has been compromised (hint: many have), or the password itself is obvious.
Some recent research has found that long or complex passwords aren’t good because people write them down or forget them. On the other hand, Ring will accept “12345678” as a password, and quite a number of other commonly used passwords that can be found on this list of stupid passwords. First piece of advice in this article: don’t use those passwords!
Ring also offers the option to register a cell phone with your account, so that when you log in, you will receive a code via SMS that you must enter to access your account. This two factor authentication (or 2FA) is stronger, and well worth the mild inconvenience, given that this is your house and its security we are talking about.
All of this is about securing your online account. The only reason that the EvilBadDoer can bother Little Johnny and take over your doorbell or security camera, at least in this moment, is that EvilBadDoer hacked your online service password to the service controls the device.

Could this marriage of IoT devices and online services be used to provide a stronger authentication? Possibly. Because a device communicates with the cloud once it’s set up, and because your phone communicates with the cloud after the doorbell is setup, it is possible for the device to provide the doorbell a token. However, for that to work, communications must be secured between the device and the doorbell during setup. Earlier this year, researchers found that this was not the case, the reason being that the doorbell was simply using unencrypted HTTP to share information about your wifi network. Bad Ring! No Ring biscuit!
Luckily, there are some onboarding standards that Ring and others could leverage to help improve matters. One is EasyConnect by the Wifi Alliance, otherwise known as Device Provisioning Protocol (DPP). Here’s how DPP works:
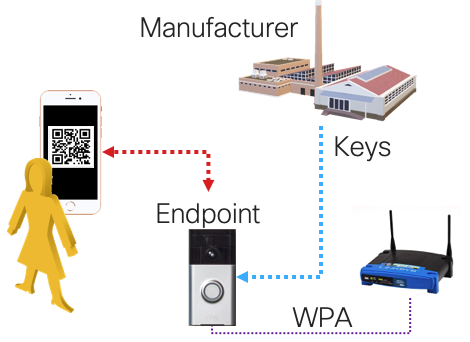
With DPP, you can use an app to scan a QR code printed on a label that came with the device that contains the public key that was installed during the manufacturing process. The app then looks for the device and authenticates using that key. Look, Ma! No passwords. DPP was primarily intended to be used for Wifi connectivity, but there’s no reason that the same trust couldn’t be leveraged to do away with Ring passwords. This is something that Amazon and others should consider.
There are some remaining challenges. For instance, what happens if you lose your phone? Can you repeat the exercise, and if you do so, would you have to do so with all the Ring devices in your house? To me this is best handled with some sort of backup before one loses one’s phone.
The key point here is that IoT can actually help itself if we adopt stronger onboarding technologies, like EasyConnect. This will take some time to get right. As a customer, you might want to ask about EasyConnect to help ease password problems so that Little Johnny can sleep easier.



