 It’s a common belief that Apple has gone to extraordinary lengths to protect individuals’ privacy through mechanisms such as Touch ID, but what are its limits? Today Forbes reported that a U.S. attorney was able to get a warrant for the fingerprints of everyone at a particular residence for the express purpose of unlocking iPhones.
It’s a common belief that Apple has gone to extraordinary lengths to protect individuals’ privacy through mechanisms such as Touch ID, but what are its limits? Today Forbes reported that a U.S. attorney was able to get a warrant for the fingerprints of everyone at a particular residence for the express purpose of unlocking iPhones.
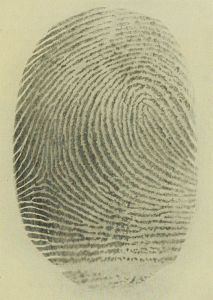
Putting aside the shocking breadth of the warrant, suppose you want to resist granting access to an iPhone. It is not that hard for someone to force your finger onto a phone. It is quite a different matter for someone to force a password out of your head. Apple has gone to some lengths to limit certain forms of attack. For instance, the Touch ID generally will not authenticate a severed finger, nor will it authenticate a fingerprint copy. Also, Apple doesn’t actually store fingerprint images, but rather hashes of the information used to collect fingerprints. Note that if the hashing method is known, then the hash itself is sensitive.
For those who care, the question is what length someone is likely to go to gain access to a phone. Were someone holding a gun to my head and demanding access to my phone, unless it meant harming my family, I’d probably give them the information they wanted. Short of that, however, I might resist, at least long enough to get to have my day in court. If that would be your approach, then you might want to skip Touch ID, lest someone simply gets rough with you to get your fingerprint. The problem is that Touch ID cannot currently be required in combination with a pass code on iPhones and iPads. Either suffices. And this goes against the a basic concept of two-factor authentication. Combine something you have, like a fingerprint, with something you know, like a pass code.
 Yesterday,
Yesterday, 